 By now it’s obvious to many that Brad Cooper was deprived of his right to a fair trial. The NC Court of Appeals agreed and ordered a new trial in September, 2013. The trial has yet to be scheduled. Through the many articles published at this blog I have tried to break down all of the evidence piece by piece so that it would be obvious that the State failed to present anything linking Brad to the crime. What was presented at trial was nothing more than twisted speculative ideas. We heard a lot of “could haves” at trial and when one examines each item independently, the evidence simply falls apart and all we are left with is the computer evidence. To really grasp the level of misconduct that occurred in this case one must take the time to understand how the computer was tampered with. It seems that many still don’t understand it and may wonder “Was the computer really tampered with? Was evidence really planted on the machine as alleged by the Defense?” . The answer of course is “Yes” and it is unmistakeable. Brad Cooper was framed. My goal is to break this down to a level where it becomes understandable to anyone who takes the time to read this. To me it is very obvious and I want others to understand it too because if it can happen to him, it can happen to any one of us at any time. For now, I would like to focus on the Google cookies.
By now it’s obvious to many that Brad Cooper was deprived of his right to a fair trial. The NC Court of Appeals agreed and ordered a new trial in September, 2013. The trial has yet to be scheduled. Through the many articles published at this blog I have tried to break down all of the evidence piece by piece so that it would be obvious that the State failed to present anything linking Brad to the crime. What was presented at trial was nothing more than twisted speculative ideas. We heard a lot of “could haves” at trial and when one examines each item independently, the evidence simply falls apart and all we are left with is the computer evidence. To really grasp the level of misconduct that occurred in this case one must take the time to understand how the computer was tampered with. It seems that many still don’t understand it and may wonder “Was the computer really tampered with? Was evidence really planted on the machine as alleged by the Defense?” . The answer of course is “Yes” and it is unmistakeable. Brad Cooper was framed. My goal is to break this down to a level where it becomes understandable to anyone who takes the time to read this. To me it is very obvious and I want others to understand it too because if it can happen to him, it can happen to any one of us at any time. For now, I would like to focus on the Google cookies.
What is a cookie?
http://www.aboutcookies.org/DEFAULT.ASPX?page=5
Basically, a cookie contains information about the individual user that enables the website to store preferences for future website visits. A cookie not only tracks information, but speeds up web browsing, because the page does not have to reload new information each time it is visited.
Why are cookies important when investigating computer evidence?
Investigators can send a subpoena to the site where the search occurred (in this case Google) and Google can supply them with:
- the IP address
- the time of the search
- date of the search
This is in fact 3rd party verification of the search — it could have proven 100% whether Brad did or did not do the search in question —- had investigators taken the time to subpoena the cookies. They did not. note: It is not possible for someone to fabricate the data in a Google cookie.
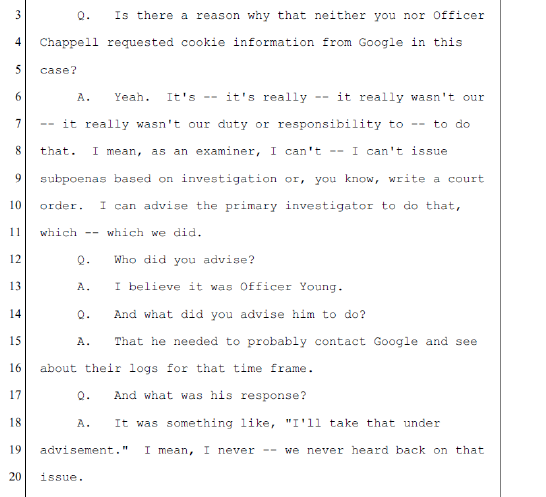
Why didn’t investigators verify the search with cookies?
State expert, Agent Johnson testified that he did advise Cary Police that it was something that needs to be done. Obviously, that recommendation was ignored.
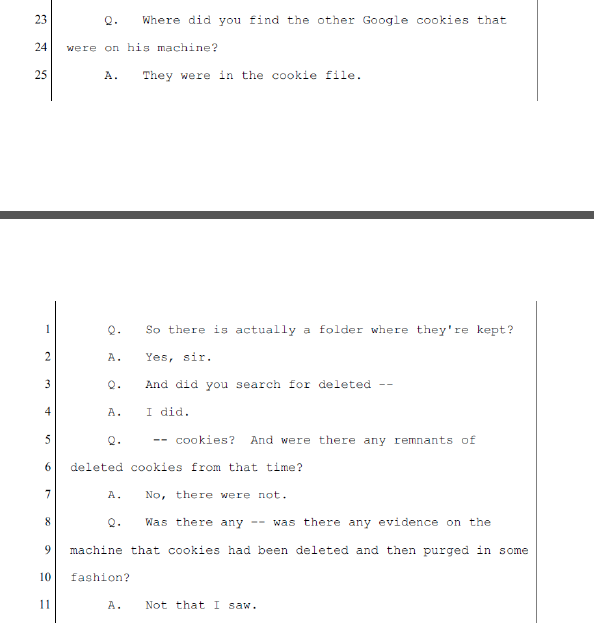
Was there a cookie that corresponded to the Google search of Fielding Drive?
No. There were no cookies at all for 7/11/08, though there were cookies for days preceding and following that date.
What explanation is there for a missing cookie?
Some have suggested that private browsing could have been used. With private browsing, no cookies are left on the hard drive. However, there would also be no temporary internet files present for private browsing searches and we know that the tif (temporary internet files) for the Fielding Drive search were present. Agent Johnson testified that private browsing was not utilized. There is no explanation for the missing cookies for 7/11/08.
Could the cookie have been deleted?
No. Agent Johnson checked and there was no sign of a deleted cookie for this search. No cookie…..no deleted cookie…..impossible for a normal search
Agent Johnson when called by the Defense —
What about Agent Chappell’s report?
Agent Chappell did in fact state in his report on computer tampering that there was a cookie that matched up to the search. During testimony, he and Agent Johnson both admitted that there was NO cookie for the Fielding Drive search. Agent Chappell, in his report, states why the cookie is so important, important enough to mention in his report. With that cookie “we have an independent way of verifying time stamps.”
Agent Chappell’s report:
Agent Chappell’s testimony:
Could investigators have sent cookies from after the alleged search time to Google to verify that the Fielding Drive search originated on Brad’s machine?
Yes, absolutely. Google cookies from 7/12/08 could have been used to identify what searches occurred on previous days.
Why didn’t the Defense subpoena Google when they received the hard drive?
Google has a privacy policy of 18 months. They only maintain IP information for that length of time and after that it is impossible to trace the search to the IP address. The State didn’t give the Defense a copy of the hard drive until just past the 18 month point — making it impossible for them to prove that Brad didn’t do the alleged search. This is despite the Defense requesting a copy earlier, and specifically notifying the police and the prosecution of Google’s privacy policy.
Why did the State wait so long to give the Defense a copy of the hard drive?
In May ’09 …. 10 months after the crime, Howard Kurtz, Brad’s defense attorney contacted Agent Johnson and asked him if he could obtain a copy of the hard drive and Johnson informed him that he was finished and that he could pick up a copy that day. Hours later, Detective Daniels contacted Brad’s attorneys and informed them that ADA Howard Cummings would not release the hard drive to them. No reason was given, no timing was given. They wouldn’t receive it until after the privacy policy had expired, making it too late to ever verify the search through Google cookies. Because they received the Defense “preservation of evidence” letter, the prosecution knew that they would miss this privacy deadline.
Is it standard for law enforcement to subpoena cookies?
Absolutely. I posted an article not long ago about another case and the very first thing investigators did was contact Google to verify the search. In fact, law enforcement in this case subpoenaed google for other irrelevant information in this case, but never for the google cookie.
Why will one never see a cookie corresponding to planted computer files?
Quite simply, it is impossible to fabricate a cookie to make it appear as though a search was performed on a particular machine. If those who framed Brad did somehow place cookies on the hard drive, if subpoenaed they would not correspond to Brad’s IP address. They would correspond to the IP address of the computer that did the search. That is why there are no cookies related to this search. This is a smoking gun indicator of planted files.
I hope this answers the questions about the significance of the absent cookies associated with this search. Of course there are several other signs pointing to tampering and the framing of Brad Cooper, but I will limit this article to the cookies alone to avoid confusion. If you are interested in learning more about everything the State did to impede the Defense’s ability to examine and then present the computer evidence at trial, please read this article.
To summarize, there is absolutely no logical explanation for the absent cookies associated with the search of Fielding Drive. This isn’t a fluke or some odd computer glitch. The temporary internet files were present and therefore the corresponding cookies should have been in the cookie folder as well.
Brad didn’t go in and delete any cookies as there were many cookies present from other days and logically, if one were to delete cookies, they would simply delete them all and certainly as a computer engineer, he would have known to delete the temporary internet files as well. I don’t know who planted the files, but it is very obvious that they were indeed planted on his machine. If the tables were turned and law enforcement and prosecutors were trying to show a Judge and jury evidence of computer tampering with evidence similar to what I’ve just described here, it would be a slam dunk case and the accused would be convicted of evidence tampering. Brad Cooper did not do the Google search of Fielding Drive. This is not a gray area….it’s crystal clear.


Wow……thanks for sharing. I hope he is able to be a free man very soon and he can see his children soon.
The tryon road mysteries seem to go unnoticed and unsolved. Brad and nancy lived off tryon road as well as jason and michell young and to mention the murder of the pregnant newspaper lady on tryon and lake wheeler at the connivence store.
Tx Kirk
>
LikeLike
Lynne…this is an excellent break down of the only piece of “evidence” cited by the jurors as the reason for his conviction. In reality, the only thing this so called “evidence” proves is that it was planted on Brad Cooper’s computer, with the Cary Police Dept & Wake County DA having full knowledge that it was, if not, they would have called Google day 1 requesting the confirmation of the originating IP address. Had they actually done that, they knew it would point in a different direction – which would be theirs!
LikeLiked by 1 person
Actually, had they used the cookies from the following day (7/12), I would imagine that they would have been able to see prior searches but there would have been no sign of the Fielding Drive search whatsoever because the search didn’t originate on the machine and there’s no cookie corresponding to it. I believe they knew this too.
LikeLike
The prosecution obviously waited until the 18 months had passed.
LikeLike
Why were these so-called law officers in such a hurry to indict and convict Brad Cooper?
LikeLike
Pressure from the “friends”, pressure from the family and a motivation to keep the safe town image. They immediately bought into Jessica Adam’s hysterics and they made their mind up right at that point that Brad was guilty and then they built the case against him and ignored all of the signs of his innocence. Classic tunnel vision and confirmation bias.
LikeLike
I believe that’s obvious too. The hard drive was ready in January ’09. Isn’t it just unbelievable that the information to prove conclusively whether Brad did the search or not was there and instead of accessing it to confirm the search they let the time expire —making it impossible to ever verify it. There are no consequences for this because they can do anything they want. It’s obvious abuse of authority.
LikeLike
Internet browsers can block cookies; to be more explicit certain browsers prompt users upon initiating a visit to a web site, asking on how to handle content (IE Cookies).
While yes it is possible these cookies were planted, it is much more likely the “cookie in question” either wasn’t found, or was never actually created, which is possible.
The arena of computers interacting with the internet and various networks is rapidly evolving, and while on day 0 information is valid and accurate on day 3 it may now be spoiled.
File times, can be it’s own specific sector of the broad stroke “digital forensics”.
LikeLike
There were cookies for the previous and subsequent days. Not a single cookie for July 11 was found.
FBI searched for evidence of deleted cookies – none found.
FBI allegedly told Cary police to subpoena Google to 3rd party verify the search. They did not.
Add all of these things together, combined with the cursor files that did not increment as they should have and it is overwhelming proof that the files were planted. Nothing suggests otherwise.
The state was so scared when the defense asked their FBI witness to duplicate the search in court – on ANY computer of his choice. Luckily for them the judge ruled for them and refused to allow it. There was one more chance to prove the tampering though. The defense asked for the print-outs of the cursor files generated when the FBI duplicated the search in their lab. State claimed it would jeopardize national security. Judge refused to compel them to show the documents! The tampering evidence is airtight. The government could convict someone of tampering based on less than this.
LikeLike
Pingback: Forensic Protocols Weren’t Followed | Justice For Brad Cooper
Utilizing something similar to “in private” or incognito browsing, which is quite easy, can impede on cookies, a simple scenario would be having not used this feature prior to the 11th, and then using it on the 11th.
Cary police not abiding by advice from the FBI about sending legal process, isn’t an indication of innocence, nor an indication of maliciousness, rather just laziness.
No evidence of deleted cookies found, to be found if no cookies were created.
Heres the thing, creating evidence which is “planted” fake spoofed, stomped; how ever you wish to put it is quite difficult.
I have for my employment created scenario’s of these measures, and of course creating the “images” or forensic backups to be used for training and testing of digital forensics examiners,
LikeLike
You need to read my book. There is no evidence that private browsing was used. Had it been used, the tif should have also been missing. There are cookies which precede and follow missing cookie #4 — the only one that would have been associated with the Google map search.
If you watch Jay Ward’s trial testimony, he shows lots of ways the files could have been planted on the machine — very easily in fact.
Lazy cops — maybe, but they weren’t too lazy to subpoena Google for Brad’s email account. Wouldn’t they want to secure their only evidence in the case against him? It appears to go beyond laziness.
You do also realize that there are multiple other signs of tampering, right? It’s not just the missing cookie.
LikeLike